Latest News
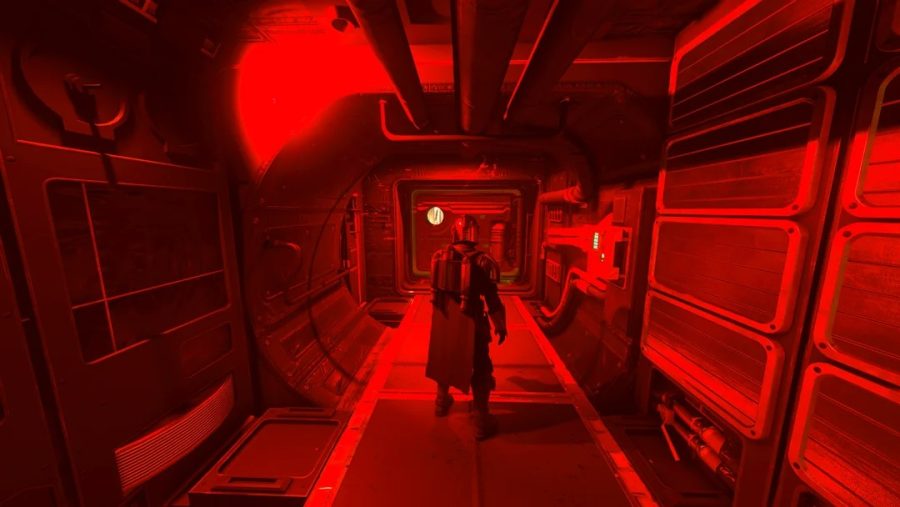
Fortnite leak – has Epic’s Battle Royale’s roadmap for 2024 been uncovered?
It should be no surprise that with Fortnite being as big as it is it seems to be the most ‘leaked-about’ games currently doing the rounds. Barely a week goes by without data miners fishing around in the code to tell everybody what skins and events are coming next. The game, which has recently seen…