Latest News
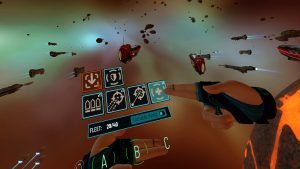
Stellar Blade reviews roundup: Critics love the gameplay and action, but not the story
Stellar Blade, the debut work from South Korea-based Shift Up, launches on April 26. The highly anticipated release is preceded by a wave of mostly positive reviews that began publishing April 24. Though most say this is a good game, few find it to be a breakthrough or transformative work, despite the pre-release clamor from…