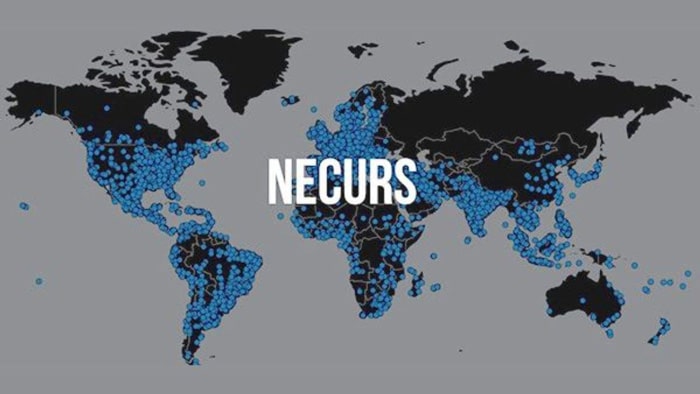
Microsoft’s Digital Crimes Unit had coordinated to take down Necurs botnet and have now done so. The name doesn’t ring a bell? Necurs was a botnet that is pretty well known in the tech world. This botnet has said to have scammed and infected more than nine million computers globally. The criminals behind this have been using several advanced strains of malware to do so. Thankfully, the botnet is now offline.
This botnet used to target potential victims through spam emails. As many people know, you can do alot to protect your devices from malware but humans will always be the weakest link. There’s anti-malware software but humans are the ones that introduce the malware to the device in the first place.
Eight years ago, Microsoft and partners across 35 other countries began tracking the botnet. They released a post detailing their operation. In the said post, it is believed that the criminals behind the botnet are based in Russia. During a 58-day period during Microsoft’s investigation, it was noticed that a Necurs-infected computer sent a total of 3.8 million spam emails to over 40.6 million potential victims. This computer has also been used to attack other computers on the internet. As well as this, they stole credentials for online accounts and stole personal information and confidential data.
What’s worse is that the criminals behind the Necurs botnet were also profiting by offering their cyber weapon as a botnet-for-hire service.
Microsoft can finally lay the finishing blow
Not too long ago, a court has enabled Microsoft to take control of US infrastructure that was being used to build the botnet and infect others with malware. After this, Microsoft took control of several domains and stops new ones from being registered. This, in effect, stopped Necurs botnet from being able to execute its cyber attacks. This was done so through Microsoft analyzing a technique that Necurs used to generate new domains via an algorithm. Microsoft were able to then successfully predict over 6 million domains. These were domains that would be generated by the botnet in the next 25 months.
Once these domains were found, they were reported to their respective registries in countries around the world so that the websites could be blocked. This then prevented more devices from becoming a part of the Necurs infrastructure. Thanks to Microsoft taking control of the already existing domains and stopping the ability to generate new ones, they have disrupted the botnet.










